Notes:
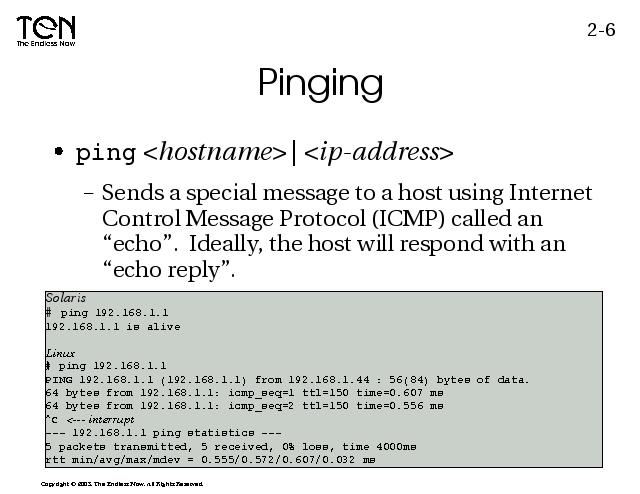
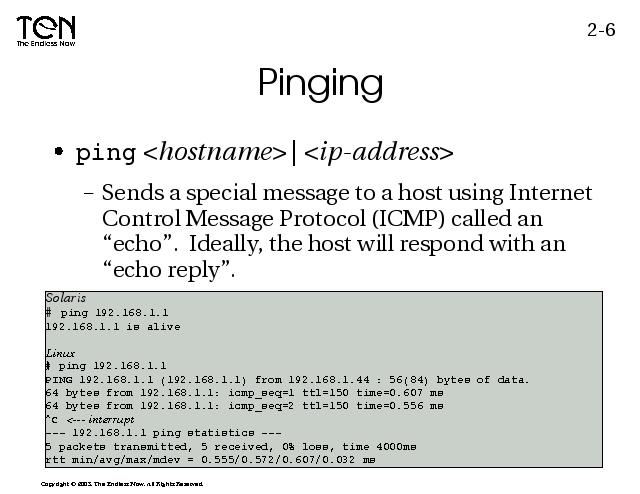
Use ping to test access to host on the network. It is common to attempt to ping the default gateway. (Some ping utilities will continue to ping the host until you interrupt the process. On hosts like Solaris, you can get this same behavior by specifying the -s option).
The ping utility sends an ICMP "echo" command. The list of ICMP command message types can be found in RFC792. Then the command waits for an "echo reply" to be sent back from the target host. It is possible, and has become more popular to disable ICMP "echo" and/or "echo reply" as a hacker prevention measure. The ping command is a popular way for a would be hacker to find live hosts on a network.
A broadcast ping, pinging a networks broadcast address...e.g. 192.168.1.255 in our case, should result in an "echo" request going to every host on the LAN (only one request goes out, but all will receive it). Then when the "echo reply" messages come back, we should see the hosts on the network. Many Unix variants provide the capability of blocking broadcast ICMP ping replies, but very few provide a means for blocking a simple ping (without installing additional software).
Normally a 1 second delay occurs between pings (may have to use -s option). Some ping implementations also allow you to ping flood (no interval between sends) a host. In some cases this could lead to a denial of service on the host being flooded. While doing a ping flood (e.g. In Linux that's -f) can be useful in assessing the reliability and possibly speed between hosts, its use is discouraged when performed on hosts without permission.